- Deutsche Telekom's Red Team disclosed a TOCTOU race in PackageKit that survived 12 years of code review.
- Two async D-Bus calls, no password, full root on Ubuntu, Debian, Fedora and Rocky Linux — CVSS 8.8, patched in 1.3.5.
TL;DR
On April 22, 2026, Deutsche Telekom's Red Team dropped Pack2TheRoot (CVE-2026-41651, CVSS 8.8) — a TOCTOU race in PackageKit's D-Bus transaction handling that lets any local unprivileged user install arbitrary packages as root. Two async calls, no password prompt, full root in about 200 ms. Affected versions span PackageKit 1.0.2 through 1.3.4 — more than twelve years of releases. Default installs of Ubuntu Desktop 18.04–26.04, Ubuntu Server 22.04–24.04, Debian Trixie 13.4, Rocky Linux 10.1 and Fedora 43 are all confirmed vulnerable. Patch: PackageKit 1.3.5.
What's new
Security researcher Vozec also published a working proof-of-concept on GitHub the same day, and the bug has its own disclosure blog on Telekom Security. What makes this one unusual is the attack surface: PackageKit is the cross-distro abstraction that GNOME Software, KDE Discover, pkcon, and RHEL's Cockpit all lean on. Anywhere you have a graphical software installer, PackageKit is probably running as a root-owned D-Bus service — and that service has been subtly broken since 2013.
Why it matters
Most recent Linux LPEs lived in a single project — Pwnkit in Polkit, Dirty Pipe in the kernel, Looney Tunables in glibc, regreSSHion in OpenSSH. Pack2TheRoot is the same class of bug but rides a D-Bus service that distros ship enabled by default on desktops and on any server that installed Cockpit for remote admin. It's the kind of bug that turns every web shell, leaked SSH key, or phished user session into instant root, without touching the kernel, without an SUID binary, without noisy exploit primitives. If you run a shared dev box, a CI fleet, a classroom Linux lab, or a Cockpit-managed VPS: every user on those systems was one shell command away from being root until April 22.
Technical facts
The bug is a three-step TOCTOU in src/pk-transaction.c:
InstallFiles()unconditionally overwrites the cached transaction flags — no check that the transaction is still in theNEWstate.pk_transaction_set_state()silently drops backward state transitions, but the flags it cached a moment ago are already mutated.pk_transaction_run()reads those cached flags lazily during idle dispatch, long after Polkit has already decided whether the caller is authorized.
The exploit fires two async D-Bus calls back-to-back, before the GLib main loop has a chance to tick:
| Step | Call | Flags presented to Polkit | Flags at execution |
|---|---|---|---|
| 1 | InstallFiles(pkg.deb) | SIMULATE — no auth required | overwritten |
| 2 | InstallFiles(pkg.deb) | already authorized | NONE — real install as root |
Polkit greenlights the simulate-only request. The daemon executes the second payload because the state machine never rolled back. The whole race fires before the idle callback; the POC wins it reliably on Ubuntu 24.04.
Proof of concept
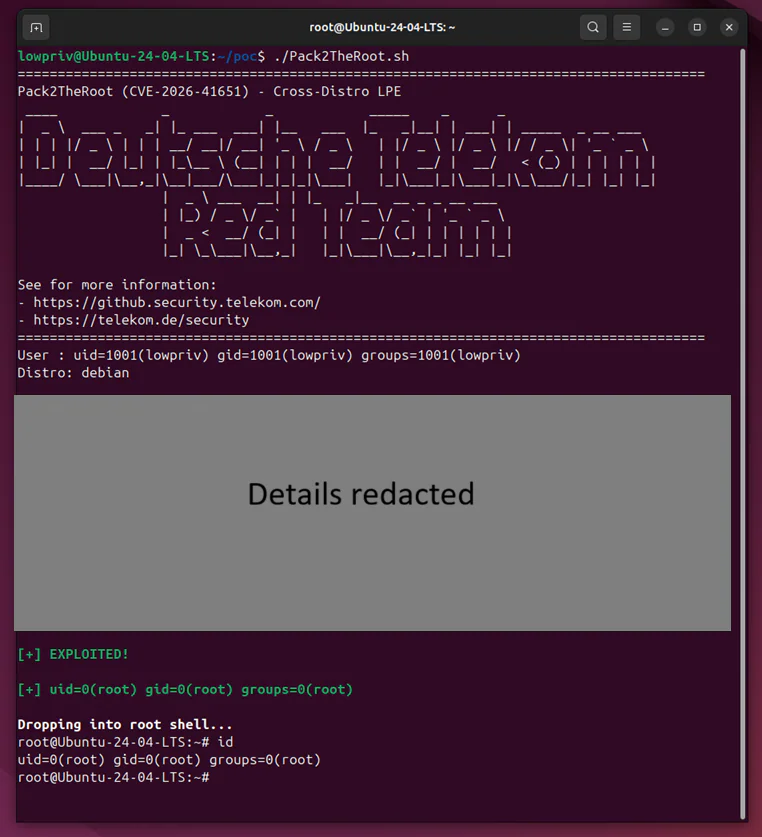
Vozec's POC takes an unprivileged shell (uid=1001), drops a crafted .deb that installs an SUID bash, and exits with euid=0(root). Time from exploit start to root shell: ~200 ms. Tested on Ubuntu 24.04 and Debian 12 with PackageKit 1.3.4 (apt and dnf backends both exploitable).
Comparison with recent Linux LPEs
| Vulnerability | Year | Component | CVSS | Needs SUID? |
|---|---|---|---|---|
| Pwnkit | 2021 | Polkit | 7.8 | Yes (pkexec) |
| Dirty Pipe | 2022 | Linux kernel | 7.8 | No |
| Looney Tunables | 2023 | glibc ld.so | 7.8 | Yes |
| regreSSHion | 2024 | OpenSSH (remote) | 8.1 | n/a |
| Pack2TheRoot | 2026 | PackageKit / D-Bus | 8.8 | No |
Use cases & who's most exposed
- Multi-user dev boxes and CI runners — any user with shell access becomes root.
- Cockpit-managed servers — even headless RHEL/Rocky boxes pull in PackageKit when Cockpit is installed.
- Desktop Linux — Ubuntu, Fedora Workstation, Debian with GNOME/KDE all ship PackageKit enabled.
- Red-team ops — reliable, distro-agnostic LPE with no kernel offsets or fragile parsing.
- Malware chaining — pairs well with any low-priv initial access (web shell, phishing payload, leaked key).
Limitations & pricing
The bug is local-only — you need an existing unprivileged session. PackageKit must be installed and enabled (true by default on every listed distro). On minimal server installs without Cockpit or a GUI, PackageKit is usually absent, so those boxes are clean. The published POC targets PackageKit 1.3.4 with apt / dnf backends; porting to yum or zypper is straightforward since the bug lives in core D-Bus logic, not the backend. No cost — it's an open CVE with a public POC.
Detection & mitigation
- Version check:
dpkg -l | grep packagekit(Debian/Ubuntu) orrpm -qa | grep packagekit(RHEL family). Anything older than 1.3.5 is vulnerable. - Post-exploit IoC: the daemon crashes with
assertion failed: (!transaction->priv->emitted_finished)atpk-transaction.c:514. Hunt withjournalctl --no-pager -u packagekit | grep emitted_finished. - Immediate workaround if you can't patch yet:
systemctl mask packagekit. Breaks GUI software installers, closes the hole. - Proper fix: upgrade to PackageKit 1.3.5. Fedora shipped
PackageKit-1.3.4-3, Ubuntu and Debian released USNs/DSAs the same day, Rocky cut RLSA-2026-8842.
What's next
Telekom has committed to publishing a deeper root-cause writeup once distros have had time to roll patches out. Expect derivative POCs targeting RHEL with Cockpit to land within days, and inclusion in linux-exploit-suggester, LinPEAS, and standard red-team toolkits shortly after. Upstream PackageKit maintainer Matthias Klumpp has hinted at a bigger refactor — making transaction flags immutable after the first Polkit authorization, killing the whole TOCTOU class rather than just this instance.
One other detail worth flagging: the Telekom advisory credits "Claude Opus by Anthropic" as an AI-assisted research tool used during discovery. It's an early, concrete example of an LLM helping find a real CVE in a widely-deployed codebase — probably not the last one you'll see in 2026.
Nguồn: Telekom Security, GHSA-f55j-vvr9-69xv, Vozec POC, oss-security.
